TL;DR:
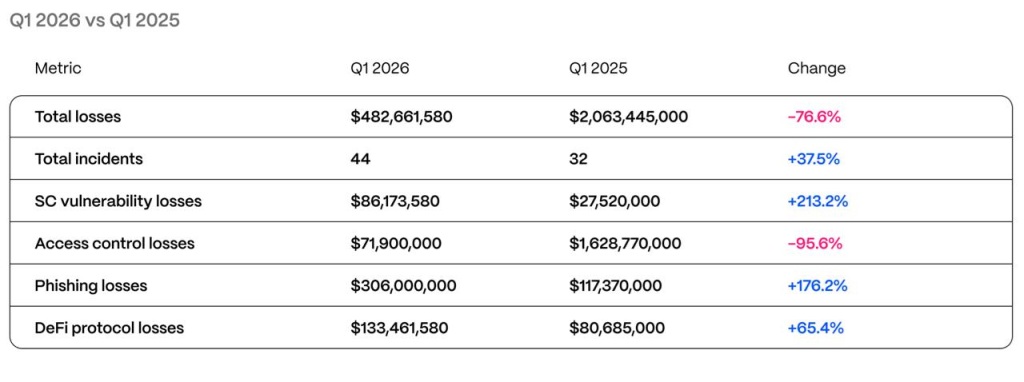
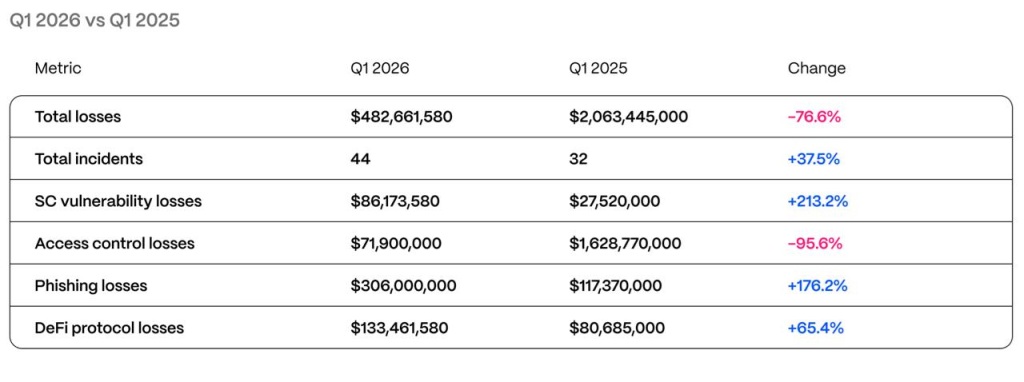
- Hacken recorded $482 million in losses throughout 44 incidents throughout Q1 2026, with phishing because the main assault vector.
- A $282 million {hardware} pockets rip-off in January accounted for greater than half of the quarter’s whole harm, in line with Hacken’s report.
- Six audited initiatives, together with Resolv with 18 audits, collected $37.7 million in losses throughout the analyzed interval.
The Web3 ecosystem misplaced $482 million in hacks and scams throughout the first quarter of 2026, in line with the quarterly report by Hacken, a agency specializing in blockchain safety. The interval recorded 44 incidents in whole, with phishing and social engineering assaults because the dominant class: $306 million in losses had been attributed solely to that vector. A single {hardware} pockets rip-off in January, valued at $282 million, concentrated greater than half of the financial harm suffered throughout the quarter.
Exploits concentrating on good contracts brought on further losses of $86.2 million, whereas entry management failures — compromised keys and susceptible cloud companies — contributed one other $71.9 million. Regardless of the dimensions, the quarter ranks as the second lowest-loss first quarter since 2023, primarily because of the absence of a catastrophic occasion similar to the Bybit hack, which in the identical interval of 2025 resulted within the theft of $1.46 billion.
Hacken: Failures Occur Exterior the Code
Yev Broshevan, CEO and co-founder of Hacken, famous that the most expensive losses “happen exterior the code layer”, in operational infrastructure that conventional audits not often cowl. The report cites the case of Step Finance, which misplaced $40 million in a pretend enterprise capital name linked to North Korean operators, and that of Resolv Labs, whose AWS keys had been compromised for $25 million.
Even the place good contracts failed, the most expensive bugs concerned legacy code: Truebit misplaced $26.4 million on account of a vulnerability in a Solidity contract deployed 5 years in the past, whereas Venus Protocol was hit by an assault sample documented since 2022.
The North Korean Menace
Hacken identifies a simultaneous tightening of regulatory frameworks comparable to MiCA and DORA within the European Union, new Singapore necessities aligned with Basel requirements together with obligatory one-hour breach notification, and the growth of powers by the Capital Markets Authority of the United Arab Emirates over digital belongings.
The agency hyperlinks these frameworks to a new infrastructure normal that features every day proof-of-reserves, everlasting onchain monitoring and automatic circuit-breakers in governance capabilities.
North Korean hacker teams are consolidating as probably the most persistent operational risk, with a playbook that mixed pretend VC calls, malicious video name instruments and compromised endpoints to extract roughly $2.04 billion from the market throughout 2025.


