Crypto wallets function your gateway to the Web3 and decentralized finance (DeFi) worlds. With no pockets, you’ll be able to’t ship, obtain, commerce, retailer, or handle your digital belongings on the blockchain. On this article, we’ll discover cryptocurrency wallets in depth, together with how they work and their differing types. We’ll additionally information you on how to decide on and arrange a pockets.
What Is a Crypto Pockets?
A crypto pockets is a bodily machine or digital answer that helps you ship, obtain, and retailer cryptocurrencies throughout blockchains. It additionally lets you purchase, promote, and handle non-fungible tokens (NFTs) and DeFi cash. Nevertheless, they don’t maintain your digital belongings instantly. They protect your personal keys, enabling safe entry to your belongings that reside on a number of blockchain networks.
Why Are Crypto Wallets Vital?
- Asset safety: Since crypto wallets securely retailer your personal keys, they guarantee solely you’ll be able to approve transactions and spend your cryptocurrencies. Many wallets have highly effective security options like two-factor authentication (2FA) and PIN to guard your funds from unauthorized entry.
- Privateness: Wallets facilitate pseudonymous cryptocurrency transactions. Although pockets actions are publicly traceable, no one can simply decode your actual identification.
- 24/7 transactions: Blockchain wallets make it easier to make crypto funds, trades, or transfers around the clock.
- Proof of possession: Each token is linked to a public handle, and solely the person with the corresponding personal key can spend it.
- Utility: Whether or not you need to have interaction in token buying and selling, staking, yield farming, or NFT minting, you could join your pockets.
How Do Crypto Wallets Work?
Crypto wallets use uneven encryption, which means they use two completely different cryptographic keys to encrypt and decrypt transactions. Therefore, if you arrange your first crypto pockets, it generates a public-private key pair.
- Personal key: It’s similar to an ATM PIN that should be stored secret. It proves asset possession and grants you the proper to entry, spend, and switch your cryptocurrencies on a blockchain. Moreover, it ensures solely you’ll be able to signal and execute transactions. Nevertheless, if any person will get maintain of your personal keys, your funds are gone endlessly.
- Public key: It’s akin to your checking account quantity, which will be shared with others to obtain funds. Your pockets handle is a shortened model of your public key and includes a random sequence of numbers and letters. As it’s mathematically derived out of your personal keys utilizing the trapdoor operate, reverse-engineering cryptographic signatures is unimaginable. Thus, no one can work out your personal keys based mostly in your public pockets handle.
Once you verify a funds switch, the transaction information is broadcast to the blockchain community. Validators/miners course of the transaction, and if verified by the community, it’ll be appended to the blockchain.
Kinds of Crypto Wallets
1. Sizzling Wallets vs Chilly Wallets
Sizzling wallets are blockchain wallets which might be linked to the web. They exist within the type of smartphone apps, browser extensions, or exchange-hosted internet wallets. They’re also referred to as on-line or software program wallets. As they facilitate speedy transactions, they’re best-suited for energetic merchants searching for comfort and quick entry to cash. Nevertheless, sizzling wallets are extremely liable to cyber threats, making them unsuitable for long-term storage.
Contrarily, chilly wallets stay offline, disconnected from the web. {Hardware} wallets, paper wallets, and airgapped units are completely different types of chilly storage. They decrease your belongings’ publicity to on-line assault vectors. Due to this fact, they supply a safer setting for storing giant quantities of crypto. Nevertheless, you could join chilly wallets to on-line units to ship crypto, making them much less handy for high-frequency merchants.
2. Custodial vs Non-Custodial Wallets
Custodial wallets are hosted and managed by third events like crypto exchanges or their custodial companions. They retailer and safe your personal keys in your behalf. They’re beginner-friendly and include quite a few built-in options, together with buying and selling interfaces and superior instruments. If you happen to lose entry to your account, you’ll be able to simply recuperate your account by password resets, electronic mail verification, and many others.
Conversely, non-custodial wallets grant you full management over your personal keys. Due to this fact, solely you’ll be able to signal transactions and restore your pockets utilizing your seed phrase. No third-party can entry, make the most of, handle, or freeze your belongings. Many self-custody wallets additionally provide an built-in DEX, NFT platform, and staking providers.
On the flip facet, custodial wallets provide customers much less management over their crypto holdings. If the pockets supplier’s platform experiences safety breaches, regulatory motion, or outages, you could lose entry to your crypto. Non-custodial wallets additionally carry inherent dangers. In case your personal keys or restoration phrases are compromised, you’ll lose your belongings completely.
3. Software program Wallets
Software program wallets are on-line functions you can obtain on varied units, together with desktops, laptops, and cell phones. They’re simple to put in and free to make use of. Nevertheless, they’re linked to the web, exposing your personal keys to cyber assaults.
Desktop wallets
If you wish to commerce cryptocurrencies out of your pc or laptop computer, desktop wallets turn out to be useful. They retailer personal keys regionally in your machine, offering you with better management over your belongings than internet wallets. Some desktop wallets combine with cryptocurrency exchanges, enabling seamless fund transfers. Nevertheless, in case your machine safety is compromised, your crypto might get stolen.
Cell wallets
Cell wallets are particularly designed to facilitate seamless transactions on the go. They’re appropriate with cellular units similar to tablets and smartphones. They’ve distinctive options like QR code scanning and face/fingerprint login to attenuate human error. Whether or not shopping for a cup of tea with crypto or buying and selling whereas travelling, cellular wallets are essentially the most handy and accessible.
Internet wallets
These wallets are accessible by internet browsers like Google Chrome and Microsoft Edge. They are often hosted or self-custody wallets.
4. {Hardware} Wallets: Safe and Offline Storage
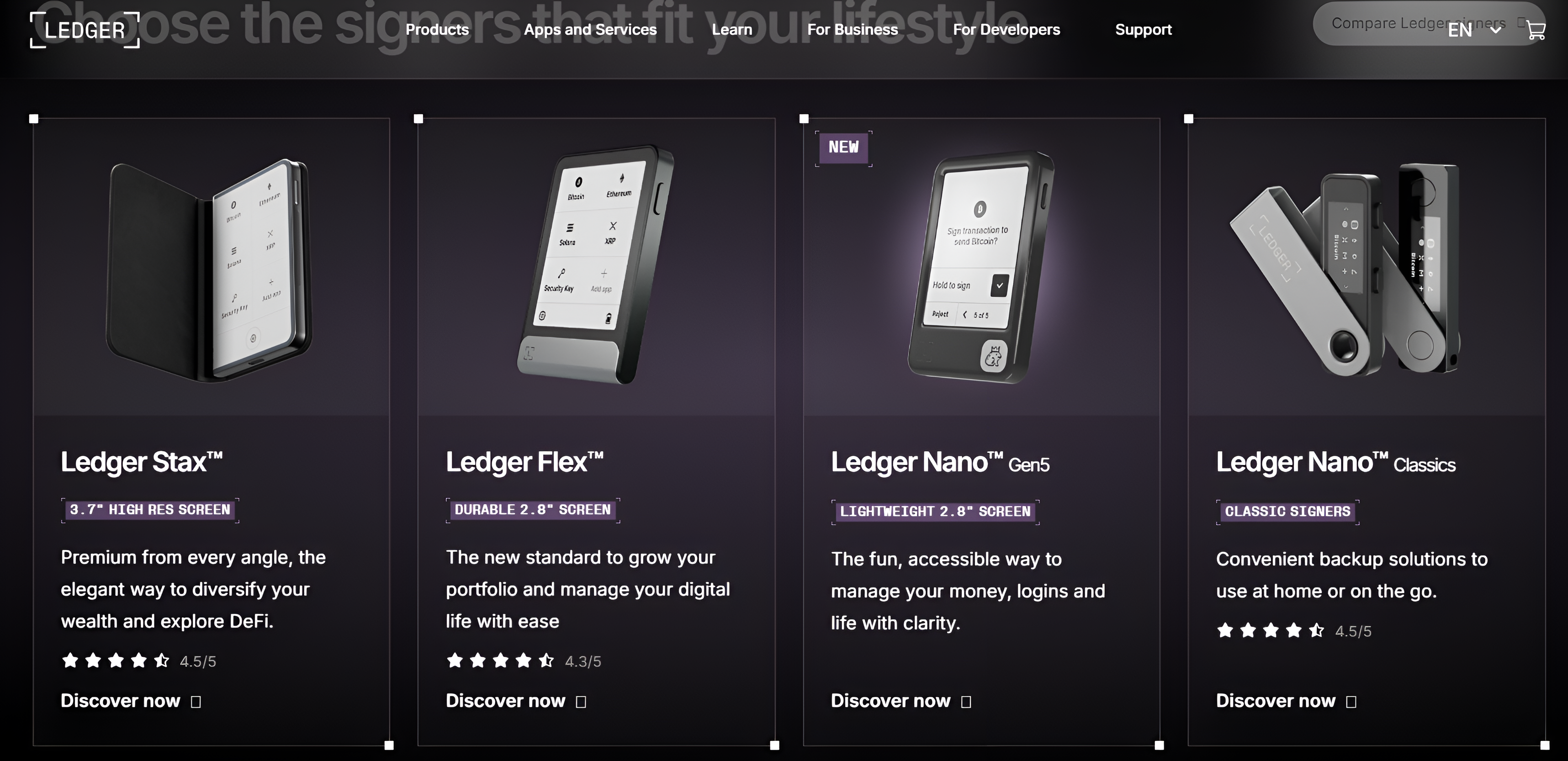
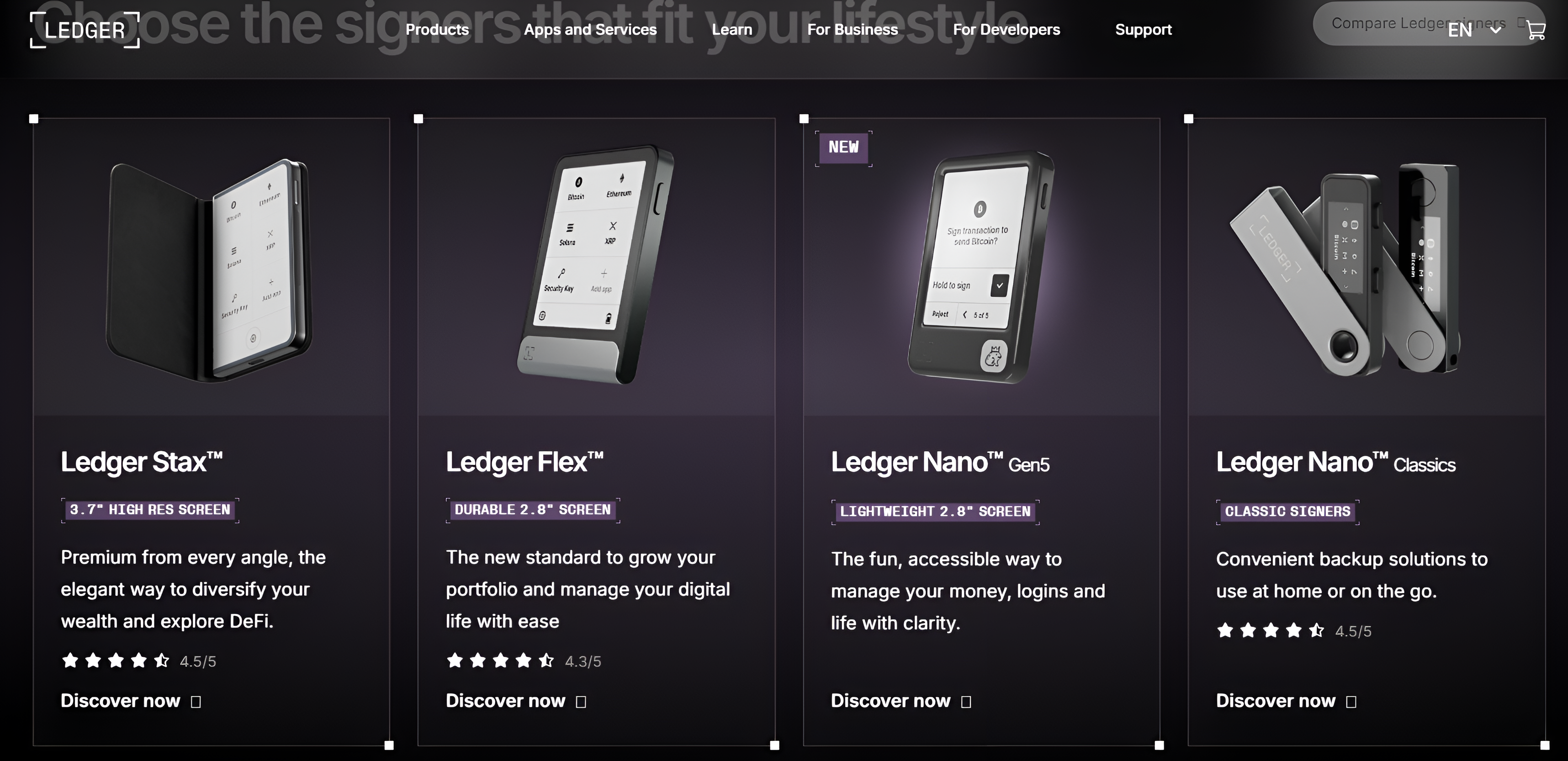
{Hardware} wallets are bodily units, typically resembling USB sticks, that retailer your personal keys offline. They’re disconnected from the web, safeguarding your belongings from hackers. Since they provide the best stage of safety on your digital currencies, they’re excellent for storing giant crypto balances.
Trezor and Ledger are essentially the most safe crypto wallets for offline storage. They protect your personal keys in a Safe Aspect chip, remoted from on-line units. These microprocessors defend your keys from a number of assault vectors, together with bodily tampering. Thus, even when your pockets falls into the mistaken palms, no one can decipher your confidential keys.
5. Paper Wallets: A Bodily Solution to Retailer Crypto
Paper wallets are bodily printouts of your private and non-private keys. They’re a kind of chilly storage equal to money or present playing cards. Nevertheless, paper degrades quick and will be simply destroyed by fireplace/water. The prints can also blur over time.
| Pockets sort | Examples |
| Sizzling/software program wallets | Metamask, Bitget Pockets |
| Chilly/{hardware} wallets | Ledger, Trezor |
| Custodial/hosted wallets | Binance change pockets, eToro |
| Non-custodial wallets | Phantom, Zengo |
| Desktop wallets | Electrum, Atomic Pockets |
| Internet wallets | Metamask, Phantom |
| Cell wallets | Exodus, OKX pockets |
The best way to Use a Crypto Pockets?
Establishing a crypto pockets
- Select a reliable pockets: Obtain a good crypto pockets app or browser extension in your desktop, laptop computer, or smartphone. Assess key parameters like security measures, ease of use, and regulatory compliance to gauge a pockets’s trustworthiness.
- Create an account: If you happen to’ve chosen a hosted pockets, furnish your fundamental particulars like e-mail, identify, and placement, and arrange a safe password. For added safety, allow 2FA through Google Authenticator or biometric verification by fingerprint/face ID.
If you happen to’ve chosen a self-custody pockets, comply with the on-screen prompts to arrange your pockets. Most non-custodial wallets don’t require customers to enter private particulars. Observe down your login credentials and seed phrase in a safe place.
- Join pockets: Hyperlink your pockets’s browser plugin with its cellular app to synchronize your belongings and transactions throughout a number of units easily.
- Fund your account: If you wish to begin buying and selling cryptocurrencies, make a crypto deposit. Most non-custodial wallets don’t permit token purchases utilizing fiat currencies. As soon as your pockets has an satisfactory steadiness, you should purchase, promote, and switch crypto.
The best way to ship and obtain cryptocurrencies utilizing a pockets?
Sending cryptocurrencies
- Log in to your pockets account/app.
- Specify the cryptocurrency you need to ship/withdraw.
- Enter the quantity to ship.
- Rigorously enter/paste the recipient handle.
- Choose the proper blockchain.
- Evaluate transaction particulars, together with charges, earlier than confirming the switch/withdrawal.
- As soon as confirmed, the transaction shall be broadcast to the blockchain community and recorded on an immutable ledger after verification.
Receiving cryptocurrencies
- Sign up to your pockets app/account.
- Select the precise token you need to obtain.
- Copy and paste your right pockets handle for deposits or scan the corresponding QR code.
- Double-check whether or not you’ve chosen the token and community appropriately.
- As soon as reviewed, share your handle with the sender.
- After the sender confirms the switch, the funds will seem in your pockets solely after the transaction is authorised on the blockchain.
The best way to again up and recuperate your crypto pockets?
In case your personal keys or {hardware} wallets are misplaced/stolen, you’ll want your restoration phrase to retrieve your pockets. Nevertheless, when the 12-24-character mnemonic phrase is compromised, it’s unimaginable to recuperate your digital belongings. Some greatest practices to securely retailer your restoration phrase are as follows:
- Write down the seed phrase precisely and retailer it in secure places similar to financial institution lockers or airgapped units.
- Engrave the phrase on metal/metallic plates.
- Keep a number of copies throughout varied geographies.
- Use Shamir backup. It creates a number of distinctive shares of your personal keys, which you’ll be able to distribute amongst trusted buddies and safe places. Every restoration share incorporates a cryptographic secret within the type of a sequence of 20 or 33 English phrases. Mix the brink variety of shares to generate the grasp seed to revive your pockets.
- Replace your wallets and backups repeatedly. Make sure the saved seed phrases haven’t develop into unreadable or inaccessible.
- By no means share the restoration phrase with anybody.
How Safe Are Crypto Wallets?
The extent of safety supplied varies throughout pockets varieties. {Hardware} wallets are the most secure as they guarantee personal keys by no means go away the offline machine and stay disconnected from the web. Software program wallets are extraordinarily susceptible to hacks, malware, and phishing, making them unfavorable for storing cryptocurrencies for prolonged intervals.
Non-custodial crypto wallets grant you freedom to handle personal keys, however the onus of securing your belongings lies solely on you. Conversely, the security of your belongings saved in custodial wallets relies on the custodian’s safety infrastructure. Custodial wallets are liable to platform points and cyber assaults that expose your cryptocurrencies to dangers of losses or theft.
For optimum safety, transfer most of your belongings into chilly wallets. Maintain solely the quantity you require for quick transactions in software program or change wallets. Lastly, evaluation your transactions earlier than confirming to attenuate handbook errors.
The best way to Select the Proper Crypto Pockets?
- Chalk out your crypto targets: Earlier than putting in/shopping for a pockets, determine whether or not you need to buy-and-hold crypto or commerce it actively. For long-term safe storage, {hardware} wallets are preferable. If you happen to’re planning to commerce constantly, sizzling or software program wallets are higher.
- Assess your buying and selling expertise: Custodial wallets are extra appropriate for newcomers. Self-custody wallets are higher for superior merchants with in-depth data of crypto storage options and related dangers.
- Safety: Select wallets with sturdy security measures like multi-factor authentication, biometric verification, passphrase safety, multi-party computation, and many others.
- Supported tokens: Choose wallets that assist the cryptocurrencies you commerce typically. If you happen to work together with DeFi protocols, purchase/promote NFTs, or bridge tokens throughout blockchains, select multi-chain wallets.
- Gadget compatibility: Go for device-agnostic wallets, ideally with a cross-platform sync function, enabling you to commerce anytime, anyplace.
- Person-friendliness: Choose wallets with a easy, clear, intuitive, and user-friendly interface.
Frequent Errors to Keep away from When Utilizing a Crypto Pockets
- Storing delicate information on-line: By no means retailer your confidential keys or mnemonic phrase on the cloud or a web based machine. Guarantee your pockets generates the seed phrase offline. Jot it down on a bit of paper or engrave it on corrosion-resistant metallic plates. You might also again it up in one other {hardware} pockets. To get rid of single factors of failure, break up the phrase and retailer every fragment throughout tamper-proof {hardware} safety modules.
- Setting a weak password: Set a posh and robust password. It serves as your first line of defence towards unauthorized entry.
- Signing crypto transactions with out reviewing: Perceive every transaction earlier than signing it. Blind signing might result in the approval of malicious transactions. Each time potential, go for clear signing.
Conclusion
Whereas every sort of crypto pockets has execs and cons, the last word alternative relies on your targets and preferences. If you happen to prioritize safety, {hardware} wallets are higher. If you happen to’re searching for comfort and quicker transactions, software program wallets are extra conducive.
FAQs
{Hardware} wallets like Trezor, Ledger, and Tangem are thought-about the most secure kinds of cryptocurrency wallets as they retailer personal keys offline. They’re disconnected from the web, defending your cryptocurrencies from on-line fraud and scams. They’re additionally superior to different types of chilly storage, like paper wallets and air-gapped computer systems.
Dropping your personal keys is akin to shedding your digital belongings endlessly, particularly in case your restoration phrase has additionally been compromised. Nevertheless, should you’ve preserved your seed phrase, you’ll be able to regenerate your personal keys. The restoration phrase serves as a grasp key that may simply restore entry to your pockets.
On-line wallets, together with change and software program wallets, are normally free. {Hardware} wallets can value something between $50 – $400.
Sure. You’ll be able to retailer a number of cryptocurrencies in a single pockets. For instance, Belief Pockets helps 100+ blockchains, facilitating cross-chain interoperability. Thus, you’ll be able to seamlessly handle belongings throughout a number of networks from a unified interface.
Sizzling wallets, together with change and software program wallets, are susceptible to on-line hacks. All kinds of offline wallets decrease your cryptocurrencies’ publicity to hackers. Nevertheless, they aren’t risk-free choices. They’re additionally inclined to bodily theft, degradation, and harm.
Bitcoin wallets are crypto wallets solely designed to retailer Bitcoin. The Bitcoin-only editions of Trezor Secure 3, 5, and seven fashions are the perfect wallets for preserving BTC.

